What are
/r/redteamsec's
favorite Products & Services?
From 3.5 billion Reddit comments
The most popular Products mentioned in /r/redteamsec:
The most popular Services mentioned in /r/redteamsec:
Dynalist
Crystal (programming language)
KeePass
Splunk
The most popular reviews in /r/redteamsec:
Hi there,
Yes - Golden SAML is a post-exploitation technique, not an infiltration technique. Post-explotation attacks can be highly useful too, like the Kerberos Golden Ticket for example (whereas Golden SAML is the SAML equivalent for it, thus it is named after it).
How attackers can gain admin access to ADFS in the first place? Usually the same as attackers get domain admin so often in corp networks. Initial infiltration using phishing or exploiting a vulnerable public facing interface (for example), lateral movement and privilege escalation using AD related techiques like pass-the-hash and many others.
This attack gained popularity lately because of its use as part of the SolarWinds attack, where a SolarWinds backdoor (aka Solorigate/Sunburst) was used to gain initial access to organizations and Golden SAML was later used for stealth user impersonation and persistence. Microsoft has published plenty of advisories on this matter.
You can't run a similar atrack by compromising a cloud IDP like Okta/Ping/AAD, because you can't steal their SAML token signing certificate. To impersonate another user in those IDPs, you would generally need to reset the user's password. But with Golden SAML (and Golden Ticket) you can impersonate any user without being intrusive, for a prolonged period.
The main added value of that advisory is basically what its headline says - exactly how to detect/hunt the attack, including the relevant event IDs. I haven't seen any other adviaory that does exactly that, except for a Splunk advisory that made a follow-up and has referenced it: https://www.splunk.com/en_us/blog/security/a-golden-saml-journey-solarwinds-continued.html
Disclosure - I work at Sygnia, the company that published this article. Hope it helped :)
So i wrote this a couple years ago as I was going through OSCP curriculum.. and only a novice myself. Take it for what it is worth. https://dynalist.io/d/mbNRBGCXctEwJqDqcoWo1HIx
But uh, there are a ton of red team workflows all over. If you can't find them effectively then life is going to be really challenging for you as a red teamer.
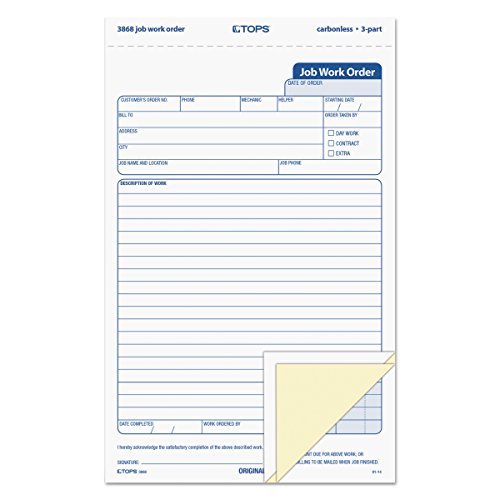
I don't do much physical stuff these days, but when I did I liked to have these with my fake clipboard to look more realistic: https://www.amazon.com/TOPS-3868-Snap-Off-Three-Part-Carbonless/dp/B0012V6ZVE
I've also always wanted an RFID cloner. The Flipper Zero project looks interesting.